Complete Visibility and Control
Over Your Agentic Workforce
Discover, understand, control, and protect every AI agent, anywhere. One install delivers full agent visibility and stops risky actions before they execute.
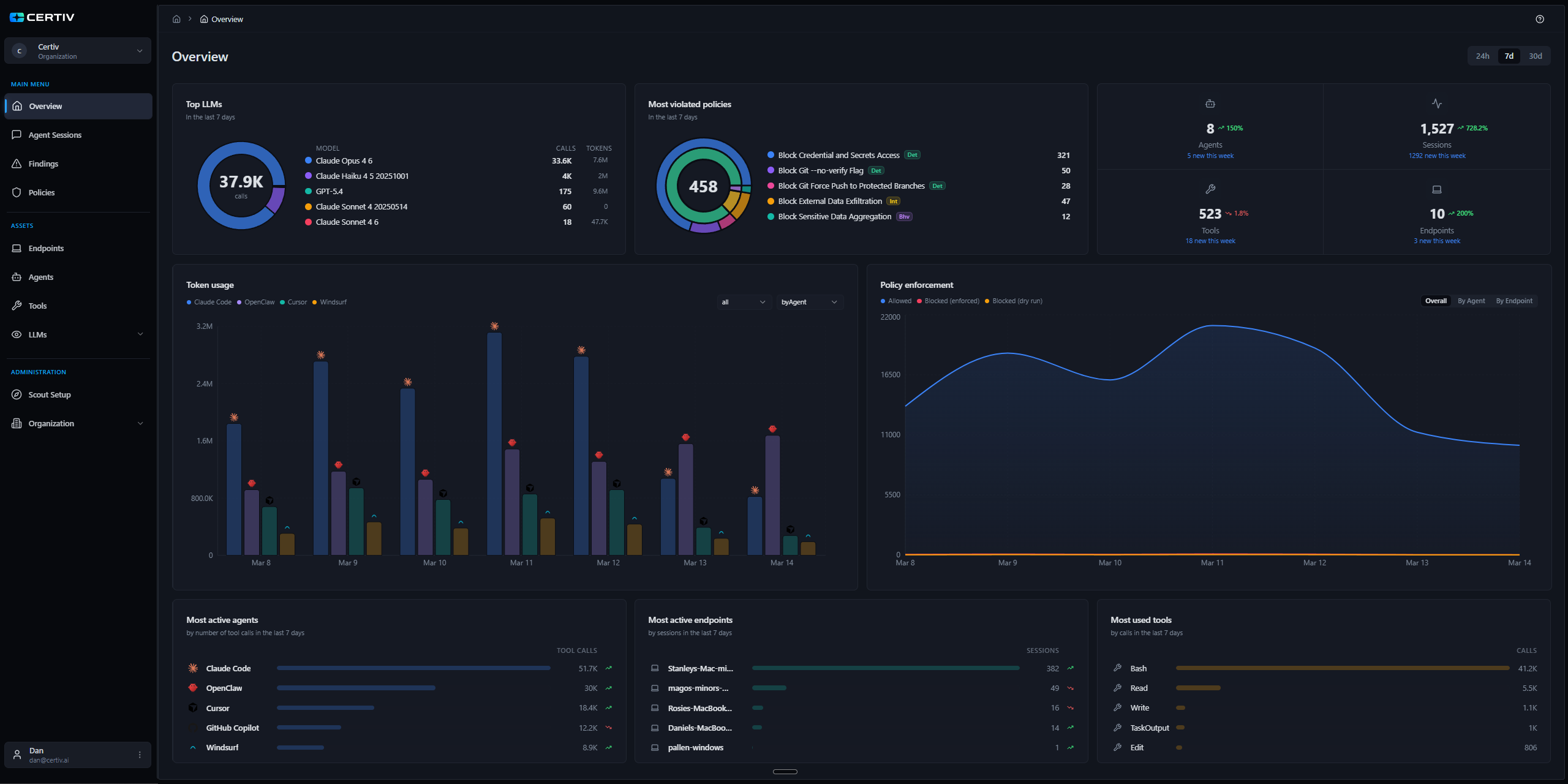
Complete Discovery and Context
Discover every agent in your environment and understand what each is doing. Certiv captures full chain-of-thought analysis, builds catalogs of endpoints, agents, tools, and LLMs, and tracks token usage and spend in real time.
Analyze agent sessions — not isolated events — to understand intent, score risk continuously, and surface behavioral anomalies before they become incidents.
"You can discover an agent, and still be completely blind."
Detect Compromised Agents in Real Time
Certiv detects agent deviations from prompt injection, credential compromise, or malicious instructions. Risk scores and flow analysis catch threats rules miss.
Certiv scores sessions against behavioral baselines. Deviations trigger blocking, incidents, and team alerts.
"The most dangerous agents are the ones that look normal. Until they don't."
Intent-Based Policy at Machine Speed
Stop risky actions before they execute. Certiv enforces intent-aware policies at machine speed, blocking or pausing dangerous actions and setting granular guardrails.
Unlike static rules, Certiv's semantic policies understand intent, not just API calls.
"If you don't control execution, you don't control agents."
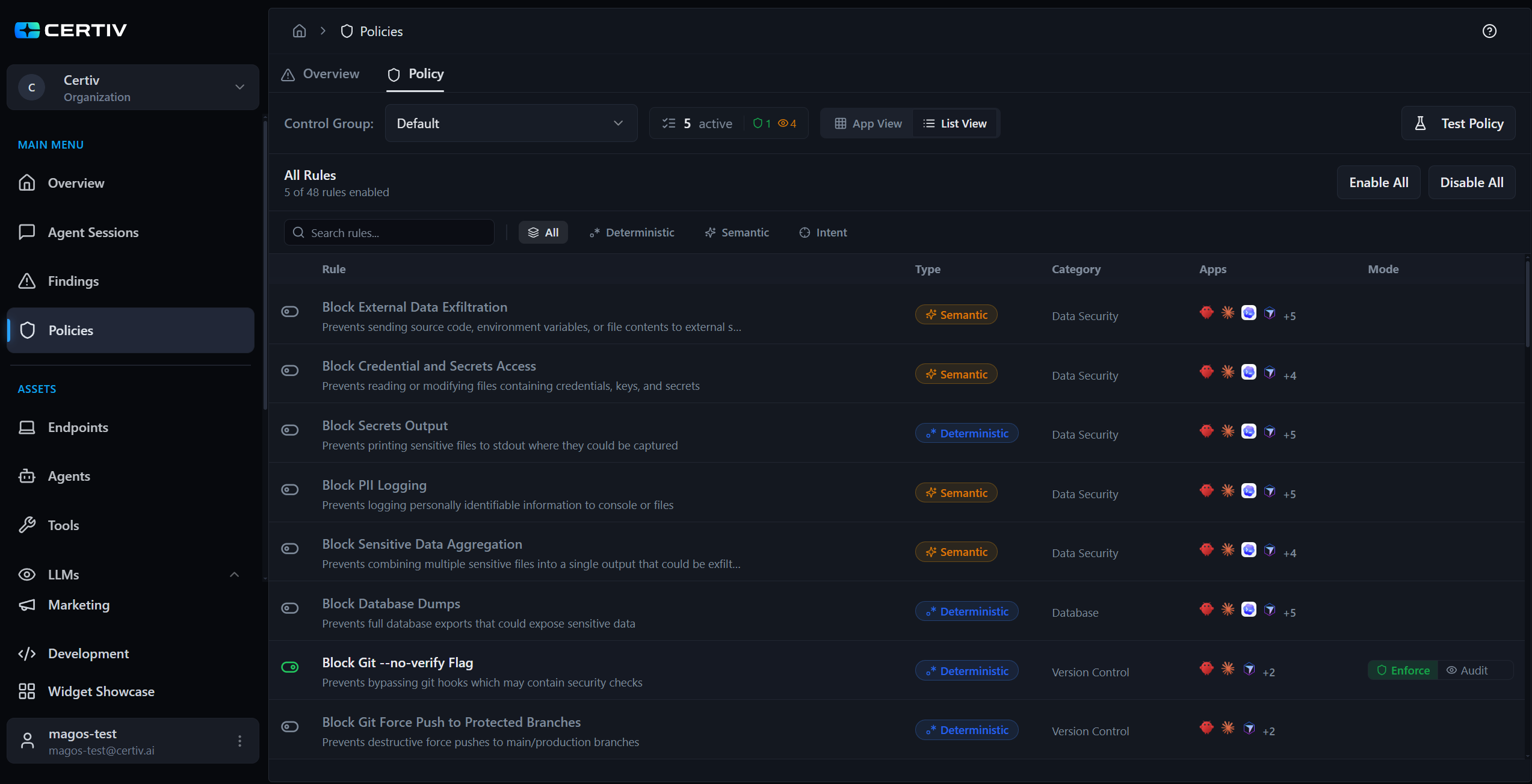
The Threats Certiv Hunts Every Day
Certiv continuously researches the evolving agent threat landscape, builds detection rules, and ships them across all your agents. Our rules are mapped to the OWASP Top 10 for Agentic Applications — and the platform is extensible so you can create your own.
Agent Goal Hijacking
Prompt injection and indirect manipulation that override an agent's intended objectives to execute attacker-controlled actions.
Tool Misuse & Exploitation
Agents calling tools in unintended ways — excessive permissions, parameter manipulation, or exploiting tool vulnerabilities.
Identity & Privilege Abuse
Agents operating with excessive permissions, impersonating users, or escalating privileges beyond their intended scope.
Supply Chain Vulnerabilities
Compromised dependencies, malicious MCP servers, poisoned plugins, and untrusted third-party agent components.
Unexpected Code Execution
Agents generating and executing arbitrary code — sandbox escapes, shell injection, and uncontrolled runtime behavior.
Memory & Context Poisoning
Manipulating agent memory, conversation history, or RAG context to influence future decisions and bypass safety controls.
Enable Agents. Enforce Policy.
Mitigate Risk.
Productivity
Business & EngineeringShip faster with guardrails, not gates
- Measure AI adoption by team, tool, and use case, not anecdotes
- Auto-approve trusted workflows with zero developer friction
- Reduce tool sprawl while driving standardization
Governance
IT & ComplianceOne control plane for every AI agent
- Discover and govern shadow AI before it becomes a security event
- Central policy surface for who, what, and where agents can act
- Audit-ready reporting for compliance, risk, and cost attribution
Security
Security & RiskStop threats before they execute
- Pre-execution controls block exfiltration, privilege abuse, and drift
- Enforce least privilege for agents, tools, and credentials
- Intent-level policy enforcement: control what agents do, not just what they access
FAQ
Frequently Asked Questions
Expand to view common questions.
Frequently Asked Questions
Expand to view common questions.
What capabilities does Certiv include?
How does Certiv deploy, and how quickly can teams get started?
Does Certiv work with any AI agent, model, or tool?
See What Your AI Agents Are Really Doing
Deploy Certiv in minutes. See every agent on your endpoints and control what happens next.